AES原理概述与算法分析:
AES属于分组加密算法,明文长度固定为128bit,密钥长度可以是128/192/256 bit,此实验分析并编码密钥为128bit的AES算法。
AES加密过程先是明文经过初始化变换,其次再经过九轮循环运算,每一次循环运算都要依次进行字节代换、行移位、列混合和轮密钥加,九轮循环运算结束后,再进行一次最终轮运算,这一轮与前面的九轮的区别除了不进行列混合,其余的不变,也即是最后一轮依次进行字节代换、行移位和轮密钥加,经过这一步骤得到的即为密文。

图1.AES加密过程
了解到整个AES的加密过程,再进一步深入分析一下各个环节的步骤。
初始变换:输入的明文矩阵与子密钥矩阵进行按字节的异或操作,得到的结果就是初始变换后的结果。
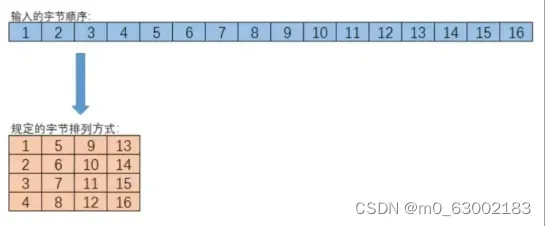
图2. 16字节数据的矩阵排列方式
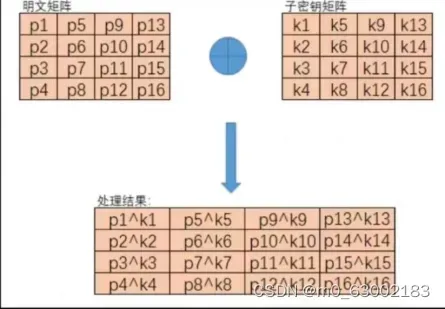
图3. 初始变换
字节代换:把4*4的矩阵通过查表进行代换,如39,即查找S盒第三行第九列的数字,将该数字替换39.
行移位:如图4所示

4. 行移位
列混合:将输入的4*4的矩阵左乘一个给定的4*4矩阵,不过不是简单的矩阵乘法运算,是在域上的运算。具体过程如下图6、7所示。

图5.列混合


图6
轮密钥加:将得到的结果与子密钥矩阵异或,一列一列逐次异或。
然而开始时只有一个16字节的子密钥,是怎么生成10轮16字节的子密钥的呢?因此,接下来分析子密钥矩阵的扩展过程。
子密钥矩阵的扩展过程:
AES的密钥扩展的目的是将输入的128位密钥扩展成11个128位的子密钥。
密钥扩展过程说明:将初始密钥以列为主,转化为4个32bits的字,分别记为w[0,1,2,3];按照如下方式,依次求解w[i],其中i是整数并且属于[4,43]。
当i%4!=0时,w[i]=w[i-4]⊕w[i-1]
当i%4=0时,将w[i-1]循环左移一个字节,分别对每个字节按S盒进行映射。与轮常量Rcon(Rc[i/4],0,0,0)进行异或,RC是一个一维数组,其中RC = {01, 02, 04, 08, 10, 20, 40, 80, 1B, 36}。最后再和w[i-1]进行异或。
解密过程是加密的逆过程,如图7所示。

图7 AES解密
其中逆字节代换是在逆S盒中实现的,而逆列混合中左乘的是。
总结:
AES算法是一种对称密码,但是这一次的对称密码比以往的实验都要复杂的多,我们在这一次实验上也花了很多的时间。
AES算法主要由四个不同的变换组成,包括一个置换和三个替代:字节代替,用一个S盒完成分组的字节到字节的代替;行移位,一个比较简单的置换;列混淆,利用域GF(28)上的算术特性的一个代替;轮密钥加,当前分组和扩展密钥的一部分进行按位XOR(异或)。
我觉得这次实验最难的一个功能模块是列混淆。因为首先列混淆的乘法不是一般的乘法,而是x乘法,即GF(2^8)上的乘法。其次这个模块涉及到矩阵运算,我们知道矩阵运算是比较复杂,比较麻烦的。该运算可以通过字节的左移一位(最后一位补0),b7=0则再与0x1B做逐比特异或来实现;若是遇到形如0x3A*0x03,则可将0x03拆成0x01异或0x02与0x3A分别相乘再进行异或。
好在本次实验矩阵的大小是4*4固定的,而且课程PPT中还给出了推导后的矩阵计算公式,使得我们不必要真的去写一个x乘法矩阵运算,只需要套用一堆固定的公式,这带来了一定程度上的方便,其中还要注意矩阵行、列计算的转换,所以还是很复杂的,很考验逻辑思维能力。
实验过程中,意识到要实现完整地AES流程是相对十分复杂的,需要提前对密钥进行密钥扩展,将明文转化成十六进制变为矩阵,加密过程中,先用初始密钥进行异或,再做九轮字节代换、行移位、列混合;最后再进行一轮字节代换、行移位的加密,加密系数高;解密过程类似,但密钥的选取倒逆选取。
个人感悟与收获:
通过这次对AES算法的代码编写,之前上课时听得不太明白的地方豁然开朗了。开始时确实是不知道从何下手,然后和队友一起讨论,两个人查阅相关的资料。每次弄懂一个知识点的时候,都不由地感叹算法的精妙。
这次实验课收获很大,不仅懂得了AES算法的核心思想,对密码学这门课也有了一定的认识,不再像之前那样毫无头绪了,对密码学也开始产生兴趣,不由地想要探索更多的知识。
经过这次实验,感觉自己对AES算法的理解、对字符字节的控制上都有所进步,收获良多。
本实验难度较大,涉及到诸多运算。但在此过程中亦收获满满。比如,了解到十六进制的x运算,该运算可以通过字节的左移一位(最后一位补0),b7=0则再与0x1B做逐比特异或来实现;若是遇到形如0x3A*0x03,则可将0x03拆成0x010x02与0x3A分别相乘再进行异或。实验过程中,意识到要实现完整地AES流程是相对十分复杂的,要提前对密钥进行密钥扩展,将明文转化成十六进制变为矩阵,加密过程中,先用初始密钥进行异或,再做九轮字节代换、行移位、列混合;最后再进行一轮字节代换、行移位的加密,加密系数高;解密过程类似,但密钥的选取倒逆选取。
代码如下:(实验环境:Visual C++ 6.0)
#include <stdio.h>
#pragma warning(disable:4996)
//定义轮常量表
static const unsigned char Rcon[10] = {
0x01,0x02,0x04,0x08,0x10,0x20,0x40,0x80,0x1b,0x36 };
//定义有限域*2乘法
static unsigned char x2time(unsigned char x)
{
if (x & 0x80)
{
return (((x << 1) ^ 0x1B) & 0xFF);
}
return x << 1;
}
//定义有限域*3乘法
static unsigned char x3time(unsigned char x)
{
return (x2time(x) ^ x);
}
//定义有限域*4乘法
static unsigned char x4time(unsigned char x)
{
return (x2time(x2time(x)));
}
//定义有限域*8乘法
static unsigned char x8time(unsigned char x)
{
return (x2time(x2time(x2time(x))));
}
//定义有限域*9乘法
static unsigned char x9time(unsigned char x)
{
return (x8time(x) ^ x);
}
//定义有限域*B乘法
static unsigned char xBtime(unsigned char x)
{
return (x8time(x) ^ x2time(x) ^ x);
}
//定义有限域*D乘法
static unsigned char xDtime(unsigned char x)
{
return (x8time(x) ^ x4time(x) ^ x);
}
//定义有限域*E乘法
static unsigned char xEtime(unsigned char x)
{
return (x8time(x) ^ x4time(x) ^ x2time(x));
}
//s盒矩阵 Substitution Table
static const unsigned char sbox[256] = {
0x63,0x7c,0x77,0x7b,0xf2,0x6b,0x6f,0xc5,
0x30,0x01,0x67,0x2b,0xfe,0xd7,0xab,0x76,
0xca,0x82,0xc9,0x7d,0xfa,0x59,0x47,0xf0,
0xad,0xd4,0xa2,0xaf,0x9c,0xa4,0x72,0xc0,
0xb7,0xfd,0x93,0x26,0x36,0x3f,0xf7,0xcc,
0x34,0xa5,0xe5,0xf1,0x71,0xd8,0x31,0x15,
0x04,0xc7,0x23,0xc3,0x18,0x96,0x05,0x9a,
0x07,0x12,0x80,0xe2,0xeb,0x27,0xb2,0x75,
0x09,0x83,0x2c,0x1a,0x1b,0x6e,0x5a,0xa0,
0x52,0x3b,0xd6,0xb3,0x29,0xe3,0x2f,0x84,
0x53,0xd1,0x00,0xed,0x20,0xfc,0xb1,0x5b,
0x6a,0xcb,0xbe,0x39,0x4a,0x4c,0x58,0xcf,
0xd0,0xef,0xaa,0xfb,0x43,0x4d,0x33,0x85,
0x45,0xf9,0x02,0x7f,0x50,0x3c,0x9f,0xa8,
0x51,0xa3,0x40,0x8f,0x92,0x9d,0x38,0xf5,
0xbc,0xb6,0xda,0x21,0x10,0xff,0xf3,0xd2,
0xcd,0x0c,0x13,0xec,0x5f,0x97,0x44,0x17,
0xc4,0xa7,0x7e,0x3d,0x64,0x5d,0x19,0x73,
0x60,0x81,0x4f,0xdc,0x22,0x2a,0x90,0x88,
0x46,0xee,0xb8,0x14,0xde,0x5e,0x0b,0xdb,
0xe0,0x32,0x3a,0x0a,0x49,0x06,0x24,0x5c,
0xc2,0xd3,0xac,0x62,0x91,0x95,0xe4,0x79,
0xe7,0xc8,0x37,0x6d,0x8d,0xd5,0x4e,0xa9,
0x6c,0x56,0xf4,0xea,0x65,0x7a,0xae,0x08,
0xba,0x78,0x25,0x2e,0x1c,0xa6,0xb4,0xc6,
0xe8,0xdd,0x74,0x1f,0x4b,0xbd,0x8b,0x8a,
0x70,0x3e,0xb5,0x66,0x48,0x03,0xf6,0x0e,
0x61,0x35,0x57,0xb9,0x86,0xc1,0x1d,0x9e,
0xe1,0xf8,0x98,0x11,0x69,0xd9,0x8e,0x94,
0x9b,0x1e,0x87,0xe9,0xce,0x55,0x28,0xdf,
0x8c,0xa1,0x89,0x0d,0xbf,0xe6,0x42,0x68,
0x41,0x99,0x2d,0x0f,0xb0,0x54,0xbb,0x16,
};
//逆向S盒矩阵
static const unsigned char contrary_sbox[256] = {
0x52,0x09,0x6a,0xd5,0x30,0x36,0xa5,0x38,
0xbf,0x40,0xa3,0x9e,0x81,0xf3,0xd7,0xfb,
0x7c,0xe3,0x39,0x82,0x9b,0x2f,0xff,0x87,
0x34,0x8e,0x43,0x44,0xc4,0xde,0xe9,0xcb,
0x54,0x7b,0x94,0x32,0xa6,0xc2,0x23,0x3d,
0xee,0x4c,0x95,0x0b,0x42,0xfa,0xc3,0x4e,
0x08,0x2e,0xa1,0x66,0x28,0xd9,0x24,0xb2,
0x76,0x5b,0xa2,0x49,0x6d,0x8b,0xd1,0x25,
0x72,0xf8,0xf6,0x64,0x86,0x68,0x98,0x16,
0xd4,0xa4,0x5c,0xcc,0x5d,0x65,0xb6,0x92,
0x6c,0x70,0x48,0x50,0xfd,0xed,0xb9,0xda,
0x5e,0x15,0x46,0x57,0xa7,0x8d,0x9d,0x84,
0x90,0xd8,0xab,0x00,0x8c,0xbc,0xd3,0x0a,
0xf7,0xe4,0x58,0x05,0xb8,0xb3,0x45,0x06,
0xd0,0x2c,0x1e,0x8f,0xca,0x3f,0x0f,0x02,
0xc1,0xaf,0xbd,0x03,0x01,0x13,0x8a,0x6b,
0x3a,0x91,0x11,0x41,0x4f,0x67,0xdc,0xea,
0x97,0xf2,0xcf,0xce,0xf0,0xb4,0xe6,0x73,
0x96,0xac,0x74,0x22,0xe7,0xad,0x35,0x85,
0xe2,0xf9,0x37,0xe8,0x1c,0x75,0xdf,0x6e,
0x47,0xf1,0x1a,0x71,0x1d,0x29,0xc5,0x89,
0x6f,0xb7,0x62,0x0e,0xaa,0x18,0xbe,0x1b,
0xfc,0x56,0x3e,0x4b,0xc6,0xd2,0x79,0x20,
0x9a,0xdb,0xc0,0xfe,0x78,0xcd,0x5a,0xf4,
0x1f,0xdd,0xa8,0x33,0x88,0x07,0xc7,0x31,
0xb1,0x12,0x10,0x59,0x27,0x80,0xec,0x5f,
0x60,0x51,0x7f,0xa9,0x19,0xb5,0x4a,0x0d,
0x2d,0xe5,0x7a,0x9f,0x93,0xc9,0x9c,0xef,
0xa0,0xe0,0x3b,0x4d,0xae,0x2a,0xf5,0xb0,
0xc8,0xeb,0xbb,0x3c,0x83,0x53,0x99,0x61,
0x17,0x2b,0x04,0x7e,0xba,0x77,0xd6,0x26,
0xe1,0x69,0x14,0x63,0x55,0x21,0x0c,0x7d,
};
//定义s盒字节代换替换操作
static void SubBytes(unsigned char* col)
{//字节代换
int x;
for (x = 0; x < 16; x++)
{
col[x] = sbox[col[x]];
}
}
//逆向字节代换
static void Contrary_SubBytes(unsigned char* col)
{
int x;
for (x = 0; x < 16; x++)
{
col[x] = contrary_sbox[col[x]];
}
}
//定义行移位操作:行左循环移位
static void ShiftRows(unsigned char* col)
{//正向行移位
unsigned char t;
//左移1位
t = col[1]; col[1] = col[5]; col[5] = col[9]; col[9] = col[13]; col[13] = t;
//左移2位,交换2次数字来实现
t = col[2]; col[2] = col[10]; col[10] = t;
t = col[6]; col[6] = col[14]; col[14] = t;
//左移3位,相当于右移1次
t = col[15]; col[15] = col[11]; col[11] = col[7]; col[7] = col[3]; col[3] = t;
//第4行不移位
}
//逆向行移位
static void Contrary_ShiftRows(unsigned char* col)
{
unsigned char t;
t = col[13]; col[13] = col[9]; col[9] = col[5]; col[5] = col[1]; col[1] = t;
t = col[2]; col[2] = col[10]; col[10] = t;
t = col[6]; col[6] = col[14]; col[14] = t;
t = col[3]; col[3] = col[7]; col[7] = col[11]; col[11] = col[15]; col[15] = t;
//同理,第4行不移位
}
//定义列混合操作
static void MixColumns(unsigned char* col)
{
unsigned char tmp[4], xt[4];
int i;
for (i = 0; i < 4; i++, col += 4)
{ //col代表一列的基地址,col+4:下一列的基地址
//xt[n]代表*2 xt[n]^col[n]代表*3 col[n]代表*1
tmp[0] = x2time(col[0]) ^ x3time(col[1]) ^ col[2] ^ col[3]; //2 3 1 1
tmp[1] = col[0] ^ x2time(col[1]) ^ x3time(col[2]) ^ col[3]; //1 2 3 1
tmp[2] = col[0] ^ col[1] ^ x2time(col[2]) ^ x3time(col[3]); //1 1 2 3
tmp[3] = x3time(col[0]) ^ col[1] ^ col[2] ^ x2time(col[3]); //3 1 1 2
//修改后的值 直接在原矩阵上修改
col[0] = tmp[0];
col[1] = tmp[1];
col[2] = tmp[2];
col[3] = tmp[3];
}
}
//定义逆向列混淆
static void Contrary_MixColumns(unsigned char* col)
{
unsigned char tmp[4];
unsigned char xt2[4];//colx2
unsigned char xt4[4];//colx4
unsigned char xt8[4];//colx8
int x;
for (x = 0; x < 4; x++, col += 4)
{
tmp[0] = xEtime(col[0]) ^ xBtime(col[1]) ^ xDtime(col[2]) ^ x9time(col[3]);
tmp[1] = x9time(col[0]) ^ xEtime(col[1]) ^ xBtime(col[2]) ^ xDtime(col[3]);
tmp[2] = xDtime(col[0]) ^ x9time(col[1]) ^ xEtime(col[2]) ^ xBtime(col[3]);
tmp[3] = xBtime(col[0]) ^ xDtime(col[1]) ^ x9time(col[2]) ^ xEtime(col[3]);
col[0] = tmp[0];
col[1] = tmp[1];
col[2] = tmp[2];
col[3] = tmp[3];
}
}
//密钥编排,16字节—>44列32bit密钥生成–> 11组16字节:分别用于11轮 轮密钥加运算
void ScheduleKey(unsigned char* inkey, unsigned char* outkey, int Nk, int Nr)
{
//inkey:初始16字节密钥key
//outkey:11组*16字节扩展密钥expansionkey
//Nk:4列
//Nr:10轮round
unsigned char temp[4], t;
int x, i;
/*copy the key*/
//第0组:[0-3]直接拷贝
for (i = 0; i < (4 * Nk); i++)
{
outkey[i] = inkey[i];
}
//第1-10组:[4-43]
i = Nk;
while (i < (4 * (Nr + 1))) //i=4~43 WORD 32bit的首字节地址,每一个4字节
{//1次循环生成1个字节扩展密钥,4次循环生成一个WORD
//temp:4字节数组:代表一个WORD密钥
//i不是4的倍数的时候
//每个temp = 每个outkey32bit = 4字节
for (x = 0; x < 4; x++)
temp[x] = outkey[(4 * (i – 1)) + x]; //i:32bit的首字节地址
//i是4的倍数的时候
if (i % Nk == 0)
{
/*字循环:循环左移1字节 RotWord()*/
t = temp[0]; temp[0] = temp[1]; temp[1] = temp[2]; temp[2] = temp[3]; temp[3] = t;
/*字节代换:SubWord()*/
for (x = 0; x < 4; x++)
{
temp[x] = sbox[temp[x]];
}
/*轮常量异或:Rcon[j]*/
temp[0] ^= Rcon[(i / Nk) – 1];
}
for (x = 0; x < 4; x++)
{
outkey[(4 * i) + x] = outkey[(4 * (i – Nk)) + x] ^ temp[x];
}
++i;
}
}
//定义轮密钥加操作
static void AddRoundKey(unsigned char* col, unsigned char* expansionkey, int round)//密匙加
{
//扩展密钥:44*32bit =11*4* 4*8 = 16字节*11轮,每轮用16字节密钥
//第0轮,只进行一次轮密钥加
//第1-10轮,轮密钥加
int x;
for (x = 0; x < 16; x++)
{ //每1轮操作:4*32bit密钥 = 16个字节密钥
col[x] ^= expansionkey[(round << 4) + x];
}
}
//AES加密函数
void AesEncrypt(unsigned char* blk, unsigned char* expansionkey, int Nr)
{//加密一个区块
//输入blk原文,直接在上面修改,输出blk密文
//输入skey:
//输入Nr = 10轮
int round;
//第1轮之前:轮密钥加
AddRoundKey(blk, expansionkey, 0);//密钥已经到位
//第1-9轮:4类操作:字节代换、行移位、列混合、轮密钥加
for (round = 1; round <= (Nr – 1); round++)
{
SubBytes(blk); //输入16字节数组,直接在原数组上修改
ShiftRows(blk); //输入16字节数组,直接在原数组上修改
MixColumns(blk); //输入16字节数组,直接在原数组上修改
AddRoundKey(blk, expansionkey, round);
}
//第10轮:不进行列混合
SubBytes(blk);
ShiftRows(blk);
AddRoundKey(blk, expansionkey, Nr);
}
//AES 解密函数
void Contrary_AesEncrypt(unsigned char* blk, unsigned char* expansionkey, int Nr)
{
int x;
AddRoundKey(blk, expansionkey, Nr);
Contrary_ShiftRows(blk);
Contrary_SubBytes(blk);
for (x = (Nr – 1); x >= 1; x–)
{
AddRoundKey(blk, expansionkey, x);
Contrary_MixColumns(blk);
Contrary_ShiftRows(blk);
Contrary_SubBytes(blk);
}
AddRoundKey(blk, expansionkey, 0);
}
int main(void) {
unsigned char pt[17], key[17];
//定义原文pt
//定义密钥key
unsigned char expansionkey[15 * 16];
int i;
int j;
printf(“You are welcome to use the AES machine in SDU\n”);
printf(“Please enter plaintext (length = 16):\n”);
scanf(“%s”, pt);
printf(“please input key:\n”);
scanf(“%s”, key);
//加密过程
ScheduleKey(key, expansionkey, 4, 10);//密钥扩展生成
AesEncrypt(pt, expansionkey, 10);//调用AES 加密
printf(“ciphertext: “);
//输出密文
for (i = 0; i < 16; i++)
{
printf(“%02x “, pt[i]);
}
printf(“\n”);
printf(“\n”);
//解密过程
Contrary_AesEncrypt(pt, expansionkey, 10);//调用AES 解密
printf(“The decrypted plaintext is: “);
//输出明文
for (i = 0; i < 16; i++)
{
printf(“%c “, pt[i]);
}
printf(“\n”);
printf(“\n”);
while (1);
return 0;
}


部分图片来源于网络,若有侵权请联系删除。如有疑问,欢迎私信。
文章出处登录后可见!
